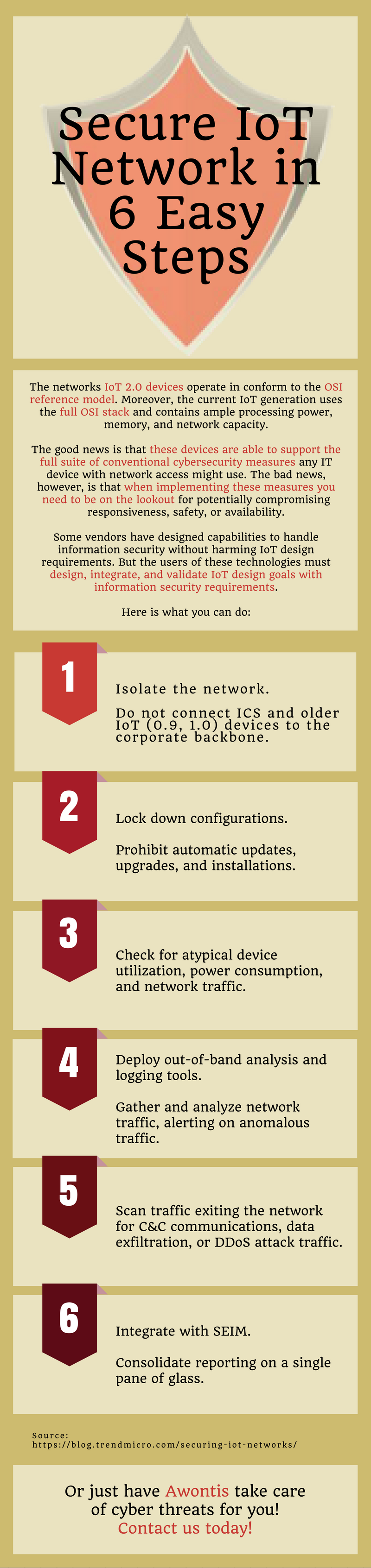
Secure IoT Network in 6 Easy Steps (Infographic)
When it comes to Industrial Control Systems operating within a customized network, one thing should be glaringly obvious – they are extremely difficult to secure. Their computing capabilities are just about enough for running their primary operating functions, but they cannot authenticate incoming messages, authorize users, log network traffic, support online updates, or use the OSI protocol stack. What is more, many use entirely proprietary, vendor-specific protocols.
So how do you secure such IoT networks? Take a look at our new infographic!