Malware: What It Is, How It Spreads, How to Defend from It
Malware – short from malicious software – is a constant threat nowadays to your personal and professional self. It attacks your computer or IT system with the intent to harm the target by corrupting your files, slowing down processes and ultimately crashing everything thus rendering you unable to use your device freely or at all. Not only that, but there are also types of malware that are meant to steal sensitive information about you, your business or both, and discredit you in front of clients or business partners – at best – or stopping all operational processes – at worst. (To see the 7 devastating effects cyber attacks can have on your business, take a look at our infographic.) If you are wondering what is what and how to protect yourself and your business against malware, stick with us!
Malware is quite a formidable threat in itself, simply because it more often than not disguises itself into clean programs allowing it to be downloaded by unsuspecting targets and staying on computers for long periods of time without the targets’ knowledge or consent.
There are several ways in which malware spreads:
- Vulnerability – A security defect in the software that can be targeted and exploited by malware (design flaw, programming error, or some other built-in weakness in the operating system, software implementation or application)
- Backdoor – An opening left in the software, hardware, system or network security for design (usually debugging purposes)
- Drive-by download – An unplanned or accidental download of malicious software from the Internet onto the computer, usually without the user’s knowledge or understanding the consequences of the act
- Homogeneity – A situation in which several computers are operated by the same system and are connected onto the same network making it easy for malware to spread from one device onto the entire system.
When it comes to business networks, malware takes even less time to spread through the system – often collapsing the entire system – and even longer to remove.
However, what is even scarier – especially to those not in the web security field – is that there are not only many subtypes of malware, but also that all of them are fast evolving.
That is why malware attacks can be performed in a number of ways:
- Exploit – A threat made real because of a successful attack on an existing vulnerability, but also a software made just for the purpose of targeting loopholes on a certain device
- Zero-day vulnerability – An undisclosed flaw hackers are able to exploit; it becomes public knowledge only when activated
- Privilege escalation – A attack where the attacker gets escalated access to a restricted level of data
- Evasion – The manner in which the malware is tailored to avoid detection and analysis by security software
- Blended threat – A mix of several types of malware aiming to explore a number of system vulnerabilities.
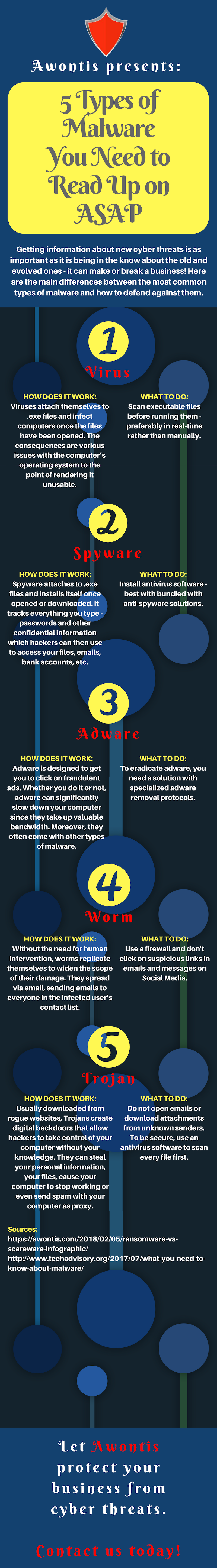
So, now that you are a little bit more familiar with how malware works, let’s brush up on what types of malware there are:
- Virus – Hidden in executable files, undetectable without specialized programs, virus multiplies until it spreads through the system and shuts it down
- Spyware – A malware used to spy on the target and collect sensitive information about and individual or entire organization without their knowledge
- Adware – Popping up as annoying ads or windows that cannot be closed, not harmful in itself, but can come with other types of malware
- Worm – Usually in existing files like email, they replicate in the system until they corrupt or destroy all files
- Trojan – Disguised as useful programs, Trojans create backdoors for unauthorized access to the infected computers to record sensitive information and use it without the knowledge or consent of the target
- Ransomware – Denies access to files and data to the target until ransom is paid, usually carries out by a Trojan
- Scareware – Simulates warnings from legitimate security programs about a large number of detected problems, but the real malware may be in the suggested solution.
Or you can just take a look at our infographics:

As you can see, the main course of action in defending your computer against malware is using anti-malware protection solutions, updating regularly (both your computer’s OS and antivirus), as well as paying attention to what you click on and download from the Internet.
As for more protection, you can count on us! We have over 275 clients who are more than satisfied with our services. On more than 1500 websites we actively monitor, nearly 55,000 security threats were successfully prevented using our solution. The websites under our protection are watched 24/7 for threats and updates, allowing the businesses they represent to thrive. Finally, the already compromised websites are fixed by being thoroughly cleaned of malicious content and protected from future threats.
Since no security threat can be removed permanently on the Internet, we will keep your defense line firm and evolving with security practices to keep you safe.

