What Are Rootkits and Rootkit Attacks?
If you’re ever at the receiving end of a rootkit attack, then you’ll understand why they are considered one of the most dangerous cyber threats today.
Rootkits are a type of malware designed to stay undetected on your computer. Cybercriminals use rootkits to remotely access and control your machine, burrowing deep into the system like a latched-on tick. Rootkits typically infect computers via phishing email, fooling users with a legitimate-looking email that actually contains malware, but sometimes they can be delivered through exploit kits.
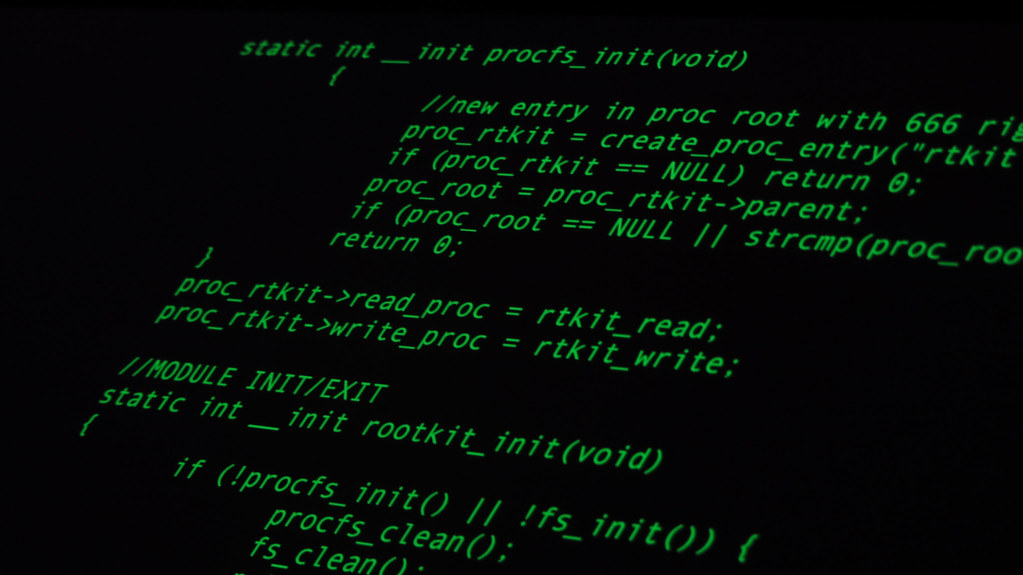
What is a rootkit?
Originally, a rootkit was a collection of tools that enabled administrative access to a computer or network. Today, rootkits are associated with a malicious type of software that provides root-level, privileged access to a computer while hiding its existence and actions. Hackers use rootkits to conceal themselves until they decide to execute their malicious malware.
In addition, rootkits can deactivate anti-malware and antivirus software, and badly damage user-mode applications. Attackers can also use rootkits to spy on user behavior, launch DDoS attacks, escalate privileges, and steal sensitive data.
Types of rootkit attacks
Attackers can install different rootkit types on any system. Below are the most common rootkit attacks.
1. Application rootkits
Application rootkits replace legitimate files with infected rootkit files on your computer. These rootkits infect standard programs like Microsoft Office, Notepad, or Paint. Attackers can get access to your computer every time you run those programs. Antivirus programs can easily detect them since they both operate on the application layer.
2. Kernel rootkits
Attackers use these rootkits to change the functionality of an operating system by inserting malicious code into it. This gives them the opportunity to easily steal personal information.
3. Bootloader rootkits
The bootloader mechanism is responsible for loading the operating system on a computer. These rootkits replace the original bootloader with an infected one. This means that bootloader rootkits are active even before the operating system is fully loaded.
4. Hardware and firmware rootkits
This kind of rootkit can get access to a computer’s BIOS system or hard drives as well as routers, memory chips, and network cards.
5. Virtualized rootkits
Virtualized rootkits take advantage of virtual machines in order to control operating systems. They were developed by security researchers in 2006 as a proof of concept.
These rootkits create a virtual machine before the operating system loads, and then simply take over control of your computer. Virtualized rootkits operate at a higher level than operating systems, which makes them almost undetectable.